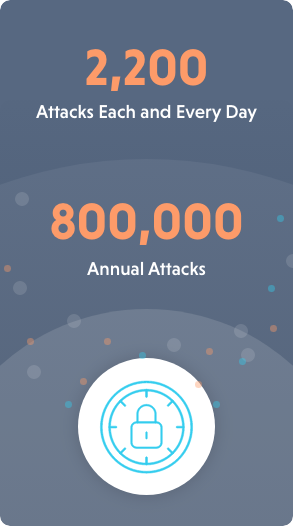
 In 2023, according to a report from Cybersecurity Ventures, there was a cyberattack every 39 seconds.
In 2023, according to a report from Cybersecurity Ventures, there was a cyberattack every 39 seconds.
That adds up to roughly 2,200 attacks each and every day, or more than 800,000 last year alone.
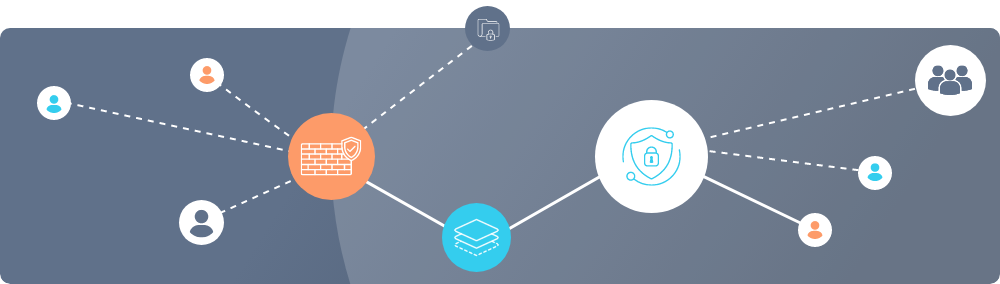
While security measures and tools are always evolving, one of the stalwarts of cybersecurity remains the network firewall — software and devices that act as a barrier between an internal network and infrastructure and external networks (like the internet).
If the internet is one big city with traffic (data) speeding along highways and streets, then firewalls are the traffic cops, monitoring the flow of traffic and determining which vehicles are allowed to enter. That makes them one of the most critical security components a company can have.
How do they work? At a high level, firewalls are a set of predefined rules and policies that dictate which incoming and outgoing network traffic is permitted or blocked.
To do this, firewalls utilize:
Packet inspection: When data packets arrive at the firewall, their headers and content is inspected.
Rule evaluation: Packets are compared against a set of rules that are configured to allow or deny traffic based on different criteria, such as its source, destination, and application.
Logging: Network firewalls often log information about the traffic they process, an invaluable process for monitoring and analyzing network activity going forward.
While security is the primary reason firewalls exist, it’s not the only one. For example, many industries are subject to regulatory requirements concerning data security, and firewalls safeguard sensitive data by controlling which devices can communicate with internal servers and databases.
Firewalls also play a big role in traffic management, ensuring critical applications receive the necessary bandwidth they need to function while preventing resource-intensive tasks from overwhelming a network.
Types of network firewalls
The first network firewalls were developed by Cisco Systems and the Digital Equipment Corporation in the 1980s. While cutting edge at the time, these initial attempts have been iterated upon substantially over the years.
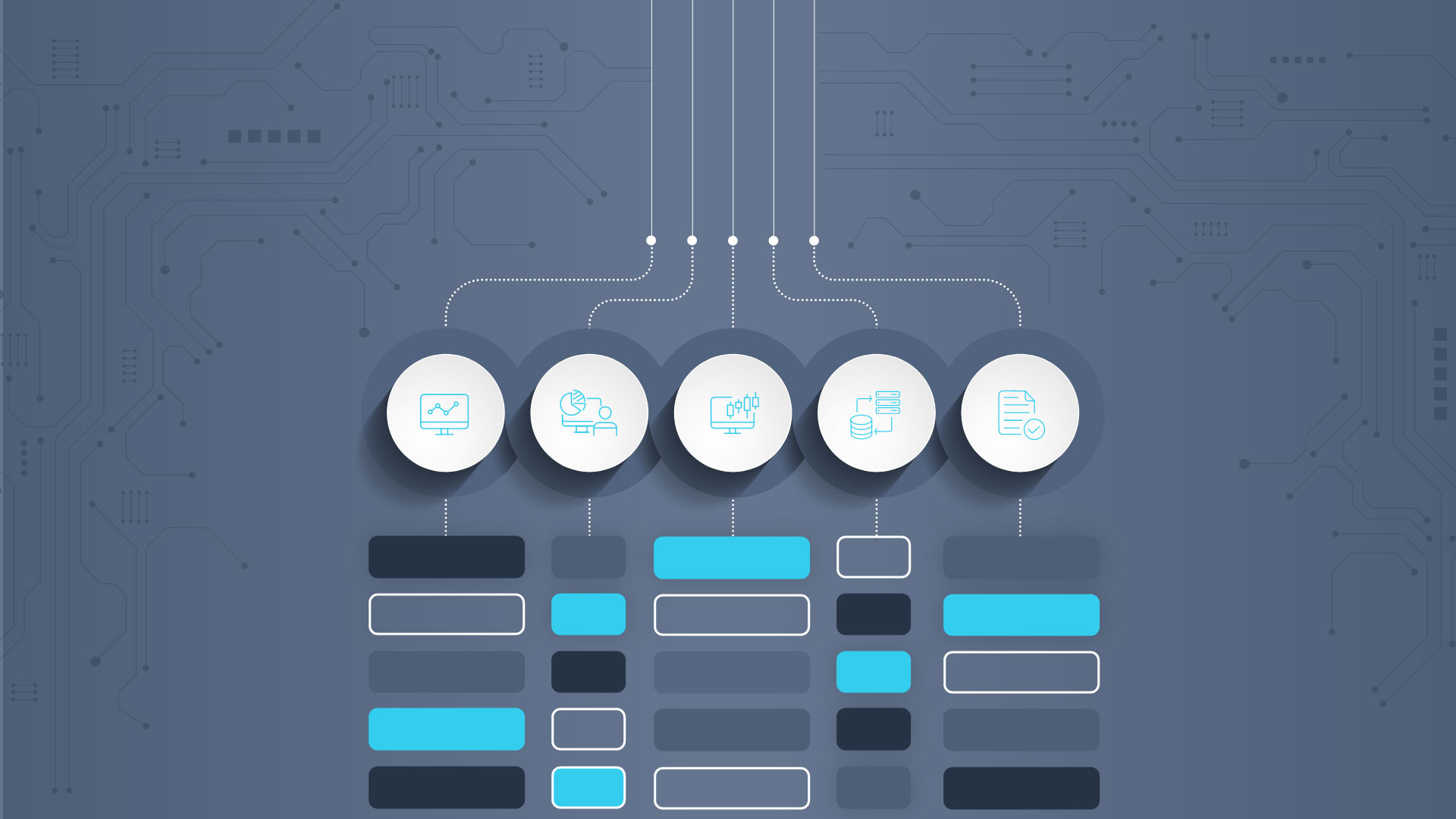
Today’s network firewalls come in several flavors, each of which has its unique characteristics and capabilities. Some of the more common ones include:
Packet filtering firewalls that operate at the network layer and make decisions based on attributes like source, destination IP address, and port numbers
Stateful inspection firewalls that combine the features of packet filtering and deep inspection, making it possible to keep track of the state of active connections to a network
Proxy firewalls that act as intermediaries between internal and external networks.
Application layer firewalls, or ALFs, that operate at the application layer to inspect and filter traffic based on specific applications and protocols.
“Next Gen” firewalls that mix traditional capabilities with advanced features like intrusion prevention, application awareness, and content filtering.
Regardless of the type of firewall your organization has in place, it’s not a “set it up and be done” tool. Firewalls need constant management, especially as your network grows and the number of connected devices expands.
Additionally, cyber threats never remain static, and as they continue to evolve you firewall rules and configurations need to be quickly updated to stay ahead of emerging threats.
Then there’s the dance between strong security and being productive. Overly strict firewall rules can block legitimate traffic and slow down your business operations, making finding the right balance an ongoing fight.
Deploying firewalls
Depending on your organization and its needs, there are a few firewall deployment strategies to choose from. These include:
Perimeter firewalls: Placed at the network perimeter (hence the name), these firewalls protect the entire internal network from external threats. In other words, they are the first line of defense.
Internal firewalls: Used to segment an internal network into zones with its own security requirements, internal firewalls provide a stronger layer of security by isolating sensitive data and limiting lateral movement for attackers within a network.
Host-based firewalls: Installed on individual devices such as laptops, host-based firewalls protect a specific endpoint.
Cloud firewalls: As the name implies, these firewalls secure cloud environments via centralized security controls for cloud-based resources and applications.
Choosing and deploying firewalls falls under the purview of IT, as does maintaining them and updating them.
IT is also tasked with monitoring network traffic for signs of suspicious or malicious activity. This is often done via intrusion detection and prevention systems (IDPS) that alert IT to potential threats so they can respond swiftly — a critical component in preventing security breaches.
Should a security breach still occur, IT takes on the role of first responder, identifying the source of the breach, assessing the extent of damage, and taking immediate steps to mitigate the impact. To do this, they may isolate affected systems, patch vulnerabilities, and conduct forensic analysis.
The final firewall responsibility of IT is user education and training. Firewalls are powerful tools, but they are only as effective as the users who interact with them. The more IT can educate employees about the importance of firewall security and best practices for safe internet usage, the stronger the firewall protection will be.