The Health Insurance Portability and Accountability Act (HIPAA) is a critical U.S. law that governs the privacy, security, and integrity of patient health information.
Enacted in 1996, compliance with the law is mandatory for healthcare providers, health plans, and businesses handling protected health information.
Among those businesses are managed IT services providers or any organization that touches a company’s IT.
HIPAA consists of several key rules:
The Privacy Rule: Sets standards for how patient health information should be accessed and disclosed.
The Security Rule: Establishes administrative, physical, and technical safeguards to ensure patient health information protection.
The Breach Notification Rule: Requires businesses to notify affected individuals, the Department of Health and Human Services (HHS), and sometimes the media if a data breach occurs.
The Enforcement Rule: Defines penalties and procedures for non-compliance.
Running afoul of any of these rules can have severe consequences for a company — even that company depended upon a managed IT services provider to ensure compliance.
For example, organizations that fail to comply with HIPAA can face substantial fines ranging from thousands to millions of dollars, depending on the severity of the violation.
Data breaches and HIPAA violations also erode trust, causing patients and clients to lose confidence in an organization’s ability to protect sensitive information.
And compliance failures can lead to audits, investigations, and mandatory corrective actions that disrupt business operations.
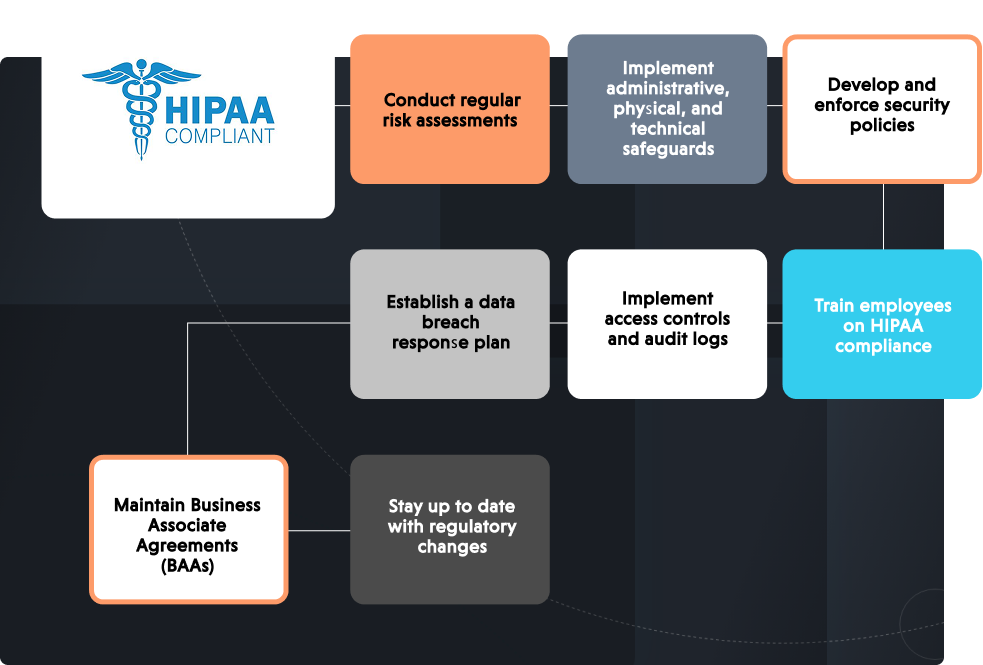
8 steps for ensuring HIPAA compliance
To achieve and maintain HIPAA compliance, organizations must adopt a proactive approach. In general, a company — or its managed IT services provider — needs to take these steps:
1. Conduct regular risk assessments
Organizations must assess potential risks to patient health information security and develop strategies to mitigate them. A thorough risk assessment identifies vulnerabilities in data storage, access, and transmission.
2. Implement administrative, physical, and technical safeguards
HIPAA requires organizations to establish specific safeguards to protect patient health information:Administrative safeguards: Policies and procedures to manage data security, including employee training and access controls.
Physical safeguards: Measures like secure facilities, access controls, and device management are used to prevent unauthorized access to patient health information.
Technical safeguards: Encryption, firewalls, and access authentication to protect electronic patient health information from cyber threats.
3. Develop and enforce security policies
Clear security policies should be documented and communicated to all employees. These policies must outline guidelines for handling patient health information, including who can access it, how it is stored, and when it can be shared.
4. Train employees on HIPAA compliance
Employees play a crucial role in HIPAA compliance. Regular training sessions should educate staff about data security best practices, phishing threats, and the importance of maintaining confidentiality.
5. Implement access controls and audit logs
Organizations should use role-based access controls (RBAC) to limit who can view and modify patient health information. Additionally, maintaining audit logs helps track data access and identify suspicious activity.
6. Establish a data breach response plan
A well-defined breach response plan outlines steps to take in case of a data breach, including investigation, notification, and corrective action measures.
7. Maintain Business Associate Agreements (BAAs)
Organizations working with third-party vendors that handle patient health information must sign Business Associate Agreements to ensure compliance responsibilities are clearly defined and upheld.
8. Stay up to date with regulatory changes
HIPAA regulations evolve with emerging threats and technological advancements. Organizations must stay informed and update their security measures accordingly.
HIPAA is too important to cut corners
HIPAA compliance is essential for protecting patient information, avoiding legal repercussions, and maintaining business integrity. While achieving compliance can be complex, organizations can implement best practices such as risk assessments, security controls, and employee training to mitigate risks.
For small and mid-sized businesses, partnering with a managed IT services provider can simplify HIPAA compliance by offering expertise, security solutions, and ongoing support.
It is critical, though, that any partner brought on for IT support — whether they’re a small IT shop or a large managed IT services provider — is both knowledgeable of what it takes to meet HIPAA rules and is in compliance themselves.