The Payment Card Industry Data Security Standard (PCI DSS) is designed to protect payment information from fraud and data breaches.
It was created by the Payment Card Industry Security Standards Council (PCI SSC), which includes big names like Visa, MasterCard, American Express, and Discover. The goal? To standardize and strengthen payment security across all businesses that handle credit card transactions.
With all those names and acronyms out of the way, here’s why you should care: If your business accepts credit card payments — online, in-person, even over the phone — you absolutely must maintain PCI DSS compliance. A failure to do so has serious consequences, including:
Data Breaches – Hackers target businesses that don’t follow security best practices, putting your customers’ sensitive data at risk.
Financial Penalties – Non-compliant businesses may face hefty fines from payment processors and credit card brands.
Legal Troubles – A security breach could lead to lawsuits, regulatory scrutiny, and major damage to your reputation.
Loss of Payment Processing Privileges – If you don’t comply, your payment processor could suspend or terminate your ability to accept credit cards.
In short: By staying compliant, you protect your customers, your business, and your bottom line —it’s that simple.
PCI compliance requirements
Like a lot of regulations, PCI compliance can be a confusing knot to untangle — especially for companies that don’t have the resources to take the DIY route. So let’s break it down.
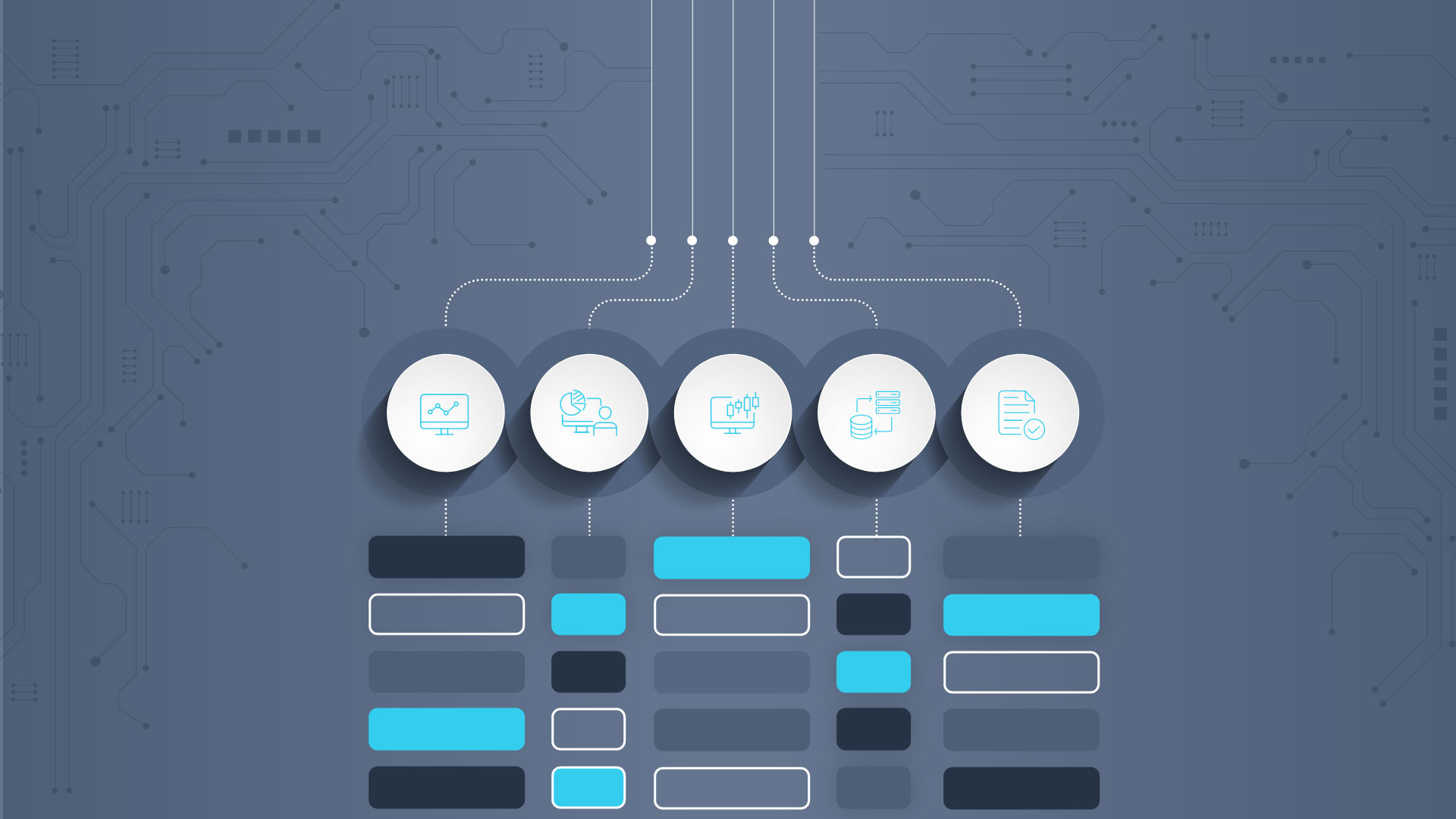
There are six major areas that make up PCI compliance. These are:
1. Secure networks
Firewalls must be installed and maintained to protect payment data, and default passwords on systems and applications must be regularly changed.
2. Cardholder data
All payment data needs to be encrypted when it is stored and when being transmitted over public networks. Encryption must be AES (128-bit or higher), RSA (2048 bits or higher), TDES/TDEA, DSA/D-H (2048/224 bits or higher), and ECC (224 bits or higher).
3. Vulnerability management
Antivirus software must be used and regularly updated, and applications must be secure.
4. Access controls
Cardholder data can only be accessed by those who absolutely need it, unique IDs for each user accessing payment need to be in place, and data storage areas must be physically secured.
5. Monitoring and testing
All access to payment systems must be tracked and logged, and regular security testing — including vulnerability scans and penetration tests — need to be regularly conducted.
6. Security policies
Every business must create and enforce a company-wide security policy that includes employee training.

Achieving PCI compliance
The good news for small and mid-sized businesses is that most won’t have to deal with regular PCI compliance audits. This is due to compliance being based on how many transactions are processed by a company.
Companies that only conduct between 20,000 and 1 million card transactions annually, for example, are able to self-assess their compliance rather than undergo a full audit.
Similarly, businesses that rely on services like Stripe, PayPal, or Square for transactions have fewer concerns, since those payment processors are on the hook for the majority of compliance requirements.
Keep in mind, though, that even if your business falls into one of the above two categories, you still need to have security measures in place.
And since most small and mid-sized businesses don’t have a dedicated security team to handle PCI compliance, going with a managed IT services provider is usually the best route.
When you work with a provider, they can help your business maintain compliance by:
- Running security assessments and vulnerability scans
- Setting up firewalls, encryption, and access controls
- Monitoring your network 24/7 for suspicious activity
- Assisting with PCI compliance paperwork and SAQ completion
- Training your team on cybersecurity best practices.
At the end of the day, PCI compliance isn’t just about checking a box—it’s about protecting your customers and your business from cyber threats.
Yes, it can feel overwhelming, but it’s manageable with the right approach.