The Dynamic Computing Team Blog
AI 101: What It Is, How to Use It, What to Watch Out For
If you’ve been paying even casual attention to the world these days, you’ve probably noticed that artificial intelligence (AI) is everywhere. It’s chock...
Insights From Our Blog
AI 101: What It Is, How to Use It, What to Watch Out For
If you’ve been paying even casual attention to the world these days, you’ve probably noticed that artificial intelligence (AI) is everywhere. It’s chock...
The Seasons of Planning
Every January, shortly after we kick off the new year, we embark on one of my favorite exercises: Annual Planning. As I wrote about last quarter, this all...
What Is a Strategic IT Partner?
If you’ve worked with an IT provider before — maybe a solo tech, a small IT shop, or even a basic managed services provider (MSP) — you’ve probably heard...
Is a Basic MSP Right for Your Business?
So your business has outgrown break/fix IT support, and the small IT shop you’ve been working with just isn’t cutting it anymore. Maybe you’re looking for...
What to Know About Partnering With an IT Shop
If you’re running a small to mid-sized business, chances are you don’t want to deal with the nitty-gritty of IT on your own. That’s why many businesses...
Pros & Cons of Relying on a Single IT Tech for Your Businesses
Most small to mid-sized businesses begin their journey with limited resources, and understandably, cost-efficiency is a top priority. One of the most...
Modernizing Your IT Systems for the New Way of Working
Let’s rewind to early 2020. Practically overnight, companies were thrown into a remote work experiment—one they didn’t exactly sign up for. Offices...
Being Intentional About Our Goals
I wish I could pinpoint when I finally figured it out. I’m sure it took me much longer than it should have. As I started my company at age 19 while in...
The Complete Guide to IT Budgeting
Technology changes. Your business changes. Even the size of your business changes.To help ensure your IT infrastructure keeps pace with all this...
Why Email Security Audits Matter (Now More Than Ever)
A lot of businesses think email security boils down to simply using strong passwords and installing spam filters, then calling it a day.But while these...
Single Sign-On: What It Is, Why It Matters, and How to Implement It
It’s 9:00 AM on a Monday. You settle into your seat, ready to dive into your day. But before you can even begin your first task, you’re already juggling a...
Understanding SOC and SIEM Solutions
No organization is immune to data breaches, ransomware, phishing, and other security challenges. As the threat landscape becomes increasingly...
Why You Need to Upgrade Windows ASAP
All technology has an expiration date. Operating systems are no exception. For Microsoft’s Windows 10, that date is October 14, 2025, when computers...
8 Steps for Creating a Disaster Recovery Plan
In business, a disaster doesn’t have to be on the scale of a category 5 hurricane. Something as simple as office sprinklers malfunctioning can be...
What You Need to Know About Business Continuity
Say your company’s servers go down due to a cyberattack. Or your offices are suddenly inaccessible due to a disaster such as fire, flood or earthquake?...
The Ins & Outs of NIST Compliance
Most cyber security frameworks can be traced back to the acronym NIST, which is short for the National Institute of Standards and Technology. This...
Don’t Cut Corners on HIPAA Compliance
The Health Insurance Portability and Accountability Act (HIPAA) is a critical U.S. law that governs the privacy, security, and integrity of patient health...
Understanding CMMC Compliance
In this era of heightened cybersecurity threats, businesses working with the U.S. Department of Defense (DoD) must take stringent measures to protect...
Knock Your Next Vendor Audit Out of the Park
Here in the Pacific Northwest, many businesses act as third-party vendors for major tech companies. One of the challenges of being in that role is...
Running the Cyber Insurance Application Gauntlet
Having cyber insurance is critical in today’s business. At the same time, simply applying for coverage is increasingly complicated. Not that long ago,...
Compliance Audits: What They Are, Why They Matter
Compliance audits may sound like a boring topic to dive into, but for small and mid-sized businesses they are a vital part of maintaining trust, security,...
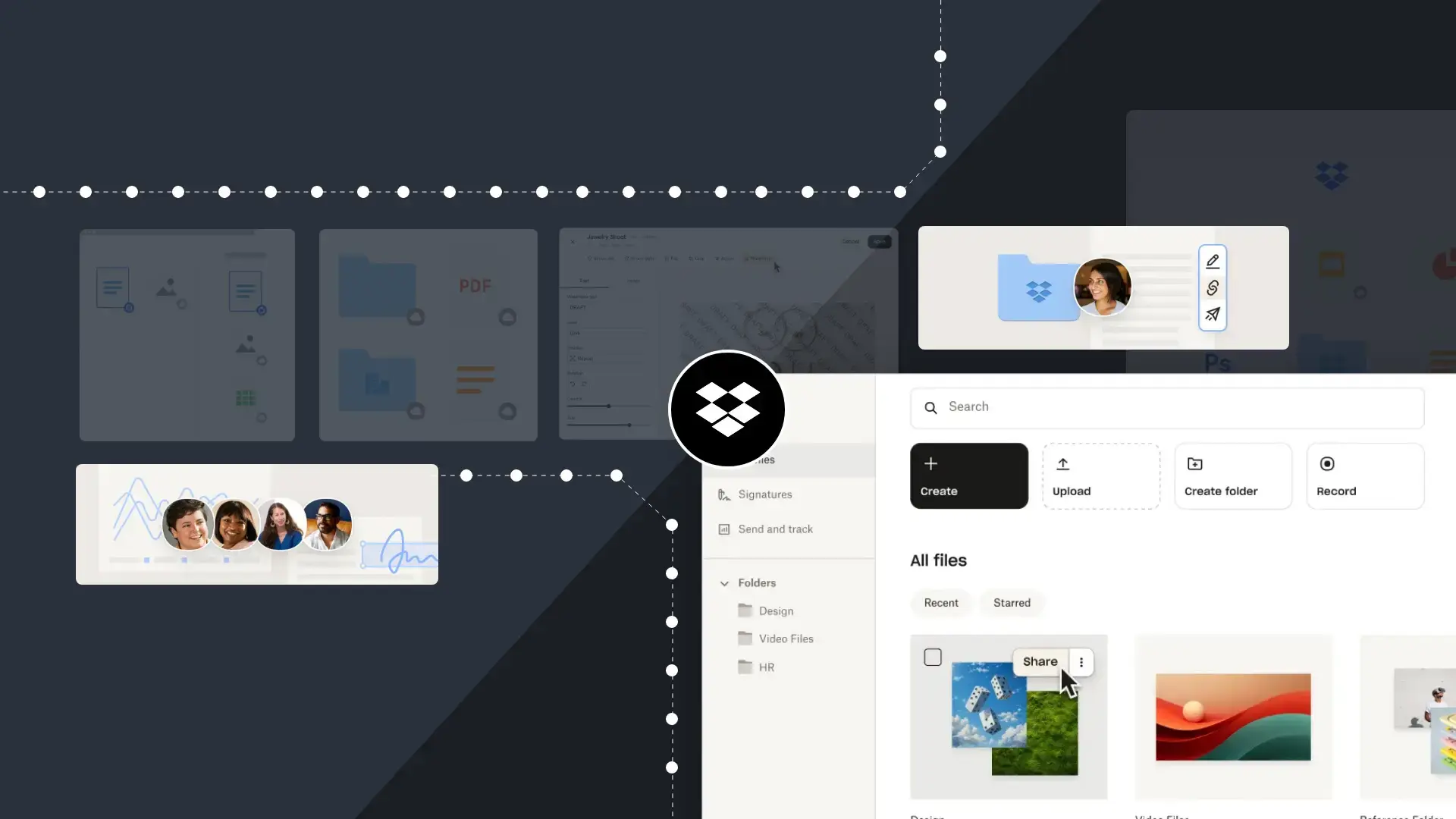
Why Dropbox Wins Compared to Other Solutions
If you're running a small or mid-sized business, there’s no shortage of tools out there to boost your productivity, collaboration, and storage. But when...
The Benefits of Dropbox Business
Whether your business is small or large, there’s a lot of choices for collaboration on the market.
6 Reasons to Use Dropbox Instead of OneDrive for Your Company Data
When you have a small or mid-sized business, every dollar counts. That means you need to safeguard your company’s data in cost-effective and efficient...
Security for Businesses of All Sizes
Think your business is too small to be the target of a cyberattack? Here are two stats that will change your mind.In the first half of 2023 alone,...
Why IT Documentation Needs Your Complete Attention
Do you know every piece of hardware your organization currently owns? What about all the software your team uses? How quickly — and smoothly — can you...
The Importance of Regular IT Business Reviews
The relationship between a company and its IT services provider is just that — a relationship.Part of that relationship is regular IT business reviews,...
Ten Reasons You Should Rely on an IT Managed Services Provider for Purchasing Your Tech
As the title of this post suggests, there are some very good reasons small and mid-sized businesses should make their IT purchases through a managed...
Our New & Improved Remote-First Normal
The pandemic was a challenging time for our team, as I’m sure it was for yours. Between the record demand for IT services, the near-constant changes to...
How to Build a Disaster Recovery Plan
The term “disaster recovery” is a bit misleading. Yes, it refers to your ability to recover from a natural or man-made calamity, but in IT, the term is...
10 Reasons Dedicated Technician Support is the Best IT Solution for Small and Mid-Sized Businesses
Every IT provider has some form of help desk support. It’s a staple of the industry. Where things differentiate, depending on the quality of IT support,...
Managing Hardware Warranty Replacement
Among the laundry list of things a small or mid-sized business owner needs to worry about, hardware warranties are usually down near the bottom.After all,...
Remote & Onsite Support
While it can be tempting for a small or mid-sized business owner to go with the cheapest IT services available, it’s important to remember that not all IT...
The Importance of Software Patch Management
When it comes to the software your company depends upon, keeping things up to date with the latest patches and fixes is critical.It’s also a much more...
Get Proactive About Preventative Maintenance
Technology can be many things. It can be powerful, efficient, and cutting-edge. It can also be finicky, prone to failure, and easily damaged.In business,...
Why Proactive System Monitoring Is Critical
Few things are as potentially destructive to small and mid-sized businesses as downtime.The loss of revenue, the reputation damage, the loss of customers...
Navigating Cyber Security Insurance
According to the Office of the Director of National Intelligence, 2023 was a watershed year for ransomware globally, with the number of attacks rising by...
Why You Need Comprehensive IT Management
It’s a simple fact that, in today’s business, your organization is only as strong as its IT.
4 Common IT Support Solutions for Businesses
Not all IT support is created equal.For small to mid-sized businesses in particular, choosing the right level of support can be a head-scratcher. Going...
What Are Managed IT Services, Really?
These days, every business needs some level of IT support. Even a custom cabinet maker toiling away in their garage has to have at least an email address,...
Cyber Security 101 for Businesses
If you own a small to mid-sized business, you’re under constant threat of a cyber attack. That’s not hyperbole. Every day, an estimated 2,200 hacks and...
The Benefits of an Audit-First Approach
Let’s talk about reaction. Not in Newton’s Third Law sense, but in technology. Specifically, being reactive in IT decision-making.Too often companies find...
Cyber Security Training: Knowing Is Half the Battle
In cyber security, the one constant is change. Bad actors are always tinkering and experimenting with new tactics to con individuals out of their...
Considering IT Outsourcing? Here's What You Need to Know
Here’s a dirty little secret about most managed IT services providers (MSPs): The more complicated they can make technology seem, the more solutions they...
The Email Line of Defense
Email has long been a favorite target of cyber criminals, with “phishing” being the most common form of attack. In fact, out of the estimated 347 billion...
10 Ways to Protect Your Business From a Cyber Attack
One of the most common errors we see small to mid-sized businesses make is a lack of focus on the basics of IT security.We get it. Security is a pain in...
Get to Know the Dark Web
The internet you interact with on a daily basis is not the entire internet. Websites you routinely visit, social media platforms you frequent, streaming...
Gone Phishing
Each day, some 347 billion emails are sent around the world. Every one of these messages has the potential to cause damage to a person or business.That’s...
The Power of Data Encryption
The numbers paint an ugly picture. According to a study, 43% of today’s cyber attacks are aimed at small and medium-sized businesses. And yet, just 14% of...
Endpoints: The First Line of Defense
The cyber security landscape is constantly changing. Every step forward in technology creates new opportunities for bad actors to poke and prod and...
Behind the Wall
In 2023, according to a report from Cybersecurity Ventures, there was a cyberattack every 39 seconds. That adds up to roughly 2,200 attacks each and every...
Minimize Headaches & Maximize Productivity
Every business relies on its IT systems running smoothly to keep employees productive and organizational goals on track. But every business has its own...
Strategic IT Planning Needs To Be at the Core
If you’re a business leader, you have a vision and strategy. It’s the core of everything you do. It was there in the beginning when you explored options,...
Upgrading Your IT Has Never Been More Critical
IT has changed dramatically in the last two decades, to say the least. We’ve seen more technological evolution in the last 18 months than we have in the...
Does Your Business Need an IT Security Audit?
From financial records to client information to valuable IP, your IT systems house highly confidential information that are crucial to your business...
How IT Procurement Impacts Your Business
Whether you’re at a business, government agency, or nonprofit organization, the process of acquiring the right IT assets will impact your business'...
Digital Transformation Consulting
Organizational IT can be complex and chaotic. As a business grows, the IT burden grows with it. New devices, systems, and software get added to the fray...
Great Onsite IT Support Makes All the Difference
When it comes to finding the right managed IT service provider, the onsite support they provide is a big difference maker. You want a provider that aces...
If You Suspect Your Account Is Hacked
Tools for Working From Home Efficiently
We're in the aftermath of the biggest social and possibly economic challenge we've faced in modern times. For those of us who are older millennials or Gen...
Benefits of Using DropBox For Architecture Project Management Software
Dropbox Business Folder and File Structure For Your Architecture Firm
Cyber Security Basics For Architecture Firms
One of the most common issues we see with potential clients is a lack of focus on IT security basics. We get it. Security is a pain in the butt. But...
Virtual Company Transformation
If you’re reading this, then we all survived. Despite the dire predictions, Seattle did not implode, and the Columbia Tower did not come crashing down....
Do You Know These 6 Latest Types of Cyber Attacks and Threats?
Security is becoming a bigger and bigger issue for small to mid-sized businesses in the Seattle area. While you may think your firm is too small to be a...
What Exactly Are Managed IT Services?
If you own a small to mid-sized business, chances are you’ve heard the words managed IT services. You’ve probably been contacted at least once by a...
Security and IT Risk
Technology is amazing! There are eye-tracking keyboards for folks with disabilities, robots that can parkour, and 3D printed houses! Unfortunately, the...
Hook, Line and Sinker: All About Email Phishing
If you have an email address, it's pretty likely you've received a phishing email. The average user receives 16 malicious emails per month, so you've...
Shadow IT is a Thing
Why Hiring Internally Rarely Solves Your IT Issues
It seems like we hear this story with a different spin on it almost every week: a company that’s grown and become more successful starts to outgrow their...

"We’ve tripled in size in the past five years, and Kevin and his team worked right alongside us. Dynamic Computing scaled their services to our growth, making sure we had exactly what we needed to work seamlessly at as a team. They set us up for success."


“Dynamic Computing understands what we need to do as a law firm. They’re keenly aware of our industry regulations and licensure requirements, and they keep our office on the cutting edge of security. They operate as part of our team to ensure confidentiality and excellence at every turn.”


“They knew that we would need more than a standard Zoom subscription to serve our clients and comply with HIPAA regulations. They transitioned us overnight to a secure telehealth system so we could continue to serve our clients.”








































.jpg?height=520&name=dynamic-digital-transformation-blog3%20(1).jpg)










.jpg?height=520&name=images-1%20(1).jpg)
.jpg?height=520&name=photo-1519615674307-877874391dc2%20(1).jpg)
